Silent Authentication and the fight against SIM Swap Fraud
By PAiCore Technology ● < 1 min read
SIM swap fraud remains one of the most damaging attack vectors across telecom and financial services, especially in emerging markets.
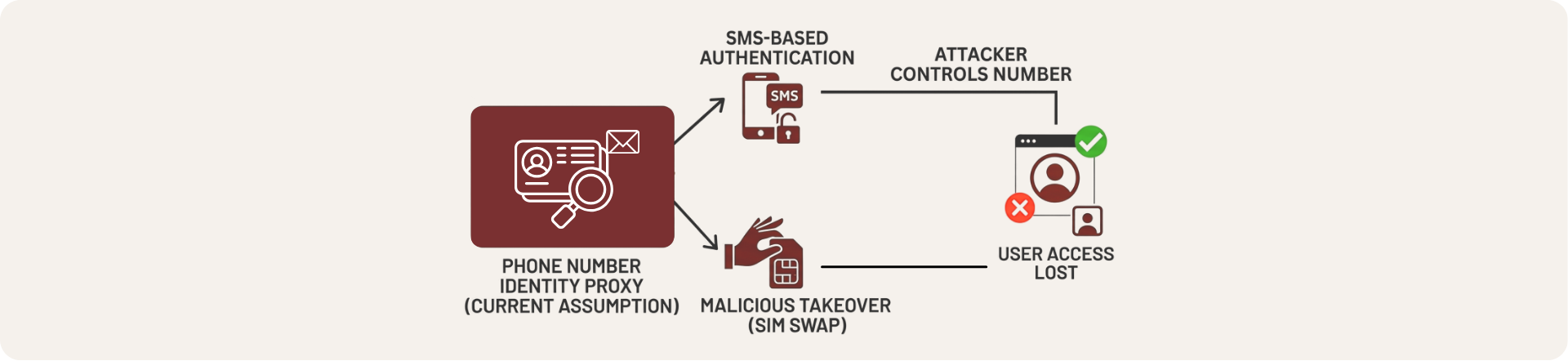
The consequences are immediate. Victims can lose access to their accounts within minutes, financial losses are often irreversible, and operators face both reputational and regulatory exposure.
At its core, most systems still treat the phone number as a proxy for identity. SMS-based authentication assumes that whoever controls the number is the legitimate user, and this is not always the case.
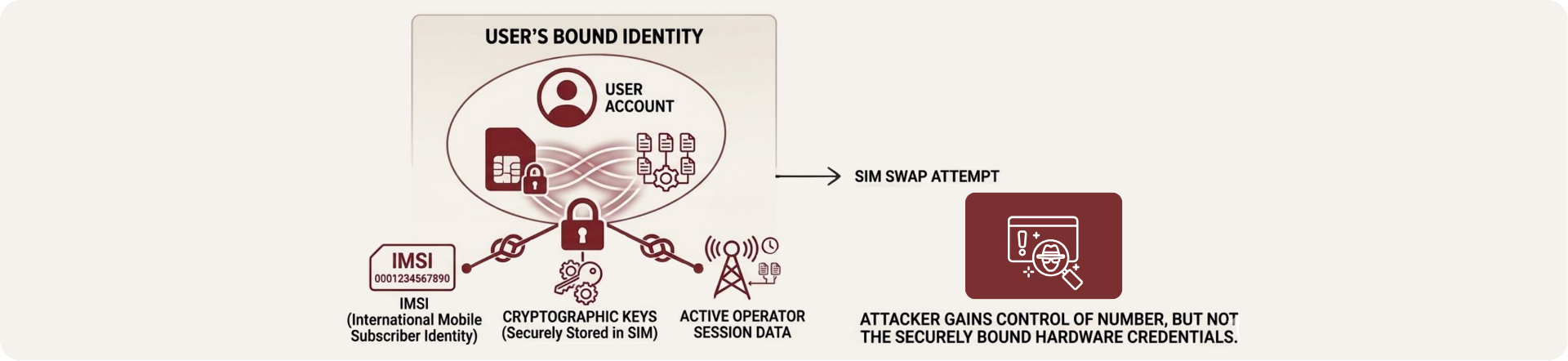
Silent authentication approaches identify validation differently. Instead of relying on the phone number, it validates the physical SIM or eSIM credentials directly within the mobile network.
This creates a binding between the user’s account and the hardware elements of their device such as the IMSI, the cryptographic keys securely stored in the SIM, and the active session data managed by the operator.
When a SIM swap occurs, the attacker may gain control of the number, but not the original hardware credentials tied to the user’s identity.
This shift is particularly relevant in regions where SIM swap fraud is more prevalent, such as Latin America, where mobile banking adoption has grown rapidly and identity verification processes are not always standardized.
Rather than adding more layers to an already fragile system, silent authentication reduces reliance on the weakest link.
