IoT devices operate differently from traditional user-driven systems, they connect, communicate, and run continuously without human input. In this context, authentication models built around passwords, OTPs, or user approvals don’t translate well into machine-to-machine environments, often adding unnecessary complexity or creating security gaps at scale.
Silent authentication takes a different path.
Instead of relying on external credentials, it uses the device’s network identity as the authentication factor. Each device, through its SIM or eSIM, carries operator-verified credentials, such as the IMSI and cryptographic keys, that are hardware-bound and cannot be replicated through software.
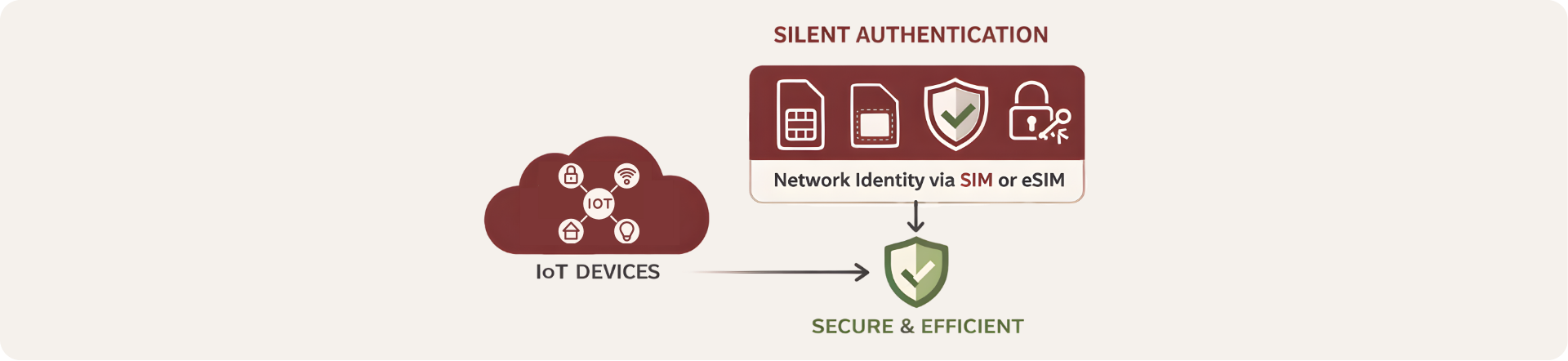
By leveraging the mobile network core, devices can authenticate directly and silently with backend systems, without any manual interaction.
For large IoT deployments, this enables:
Zero-touch provisioning
Continuous device verification
Scalable authentication without credential management overhead
Less friction, fewer moving parts and a model that aligns better with how IoT actually works.
