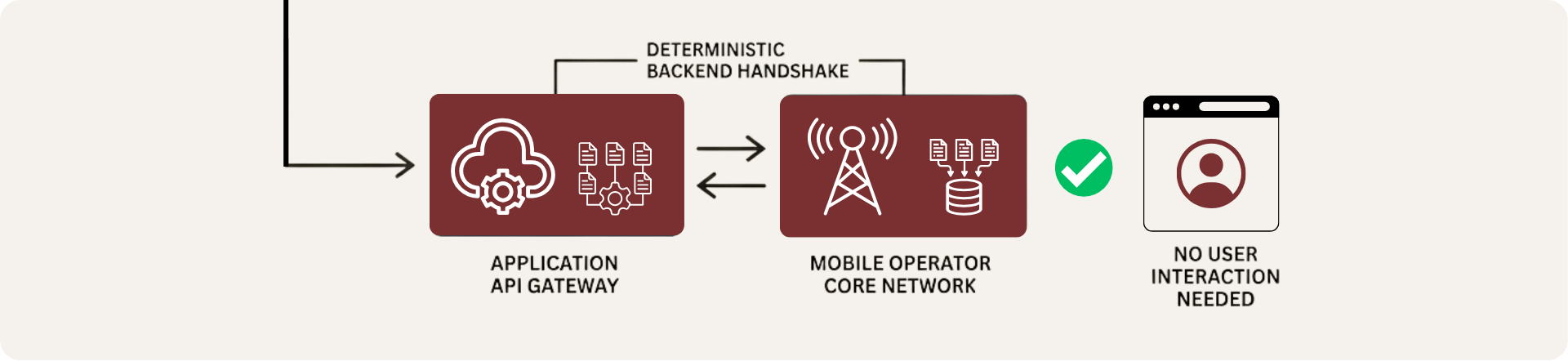
Silent Authentication is more than just a UI enhancement; it is a technical orchestration occurring within the deep layers of the network. While the user experiences instantaneous validation, the system executes a deterministic backend handshake between the application’s API Gateway and the mobile operator’s Core Network, completely removing the need for human interaction.
This process relies on robust signaling protocols that directly query the telecommunications infrastructure through the following mechanisms:
AAA Protocols (Diameter/Radius)
Establishing secure, direct communication with the operator’s authentication servers.
EAP-AKA Challenge
Generating a cryptographic challenge that only the physical SIM card can resolve, uniquely linking identity to actual hardware.
Real-time Validation
Confirming that the active data session matches exactly with the subscriber registered in the network core.
By operating at the network layers (Layer 3/4), this method is immune to application-level attacks, such as trojans designed to intercept SMS. Security shifts from a “shared secret” prone to human error to a foundation of physical device possession and cellular network integrity, effectively neutralizing critical vectors like SIM swapping and phishing.
The Backend Handshake simplifies digital trust. By moving verification to the network, it creates a seamless security model that turns a major point of friction into a reliable, invisible experience.
